This was not just about advertising. Fake LinkedIn and social media profiles were created. They were then used to connect to people and promote the ads. The details given by Confiant dwarf the known scale of Russian meddling in US and other elections in 2016 and 2017.
The end result of Zirconium’s campaign is to heap significant damage on the online advertising market. It also exposes just how easy it is for bad actors to use social media to further their ends. In addition, it has led the Google Chrome team to block the technique, forced redirects, in today’s release of Chrome-64. How quickly other browser providers will respond is unclear and Confiant has offered no details.
Zirconium has taken advantage of a technique known as forced redirect. It is used to send a person to a different website to the one they are on. According to Dangu: “Usually the website they are redirected to is a vehicle for some form of affiliate fraud or malware.” Such actions are difficult for security software to identify and therefore effective from a malware campaign perspective.
How did Zirconium do this?
Zirconium created a fake ad agency called Beginads which established relationships with ad platforms. It was first seen by Confiant in March 2017 as a stand-alone server. Dangu says that it evolved into the domain running the traffic direction system (TDS) for all Zirconium’s fake ad agencies.
The key to Zirconium’s success was its business plan. It looked at both the supply side (user traffic) and the demand side (landing pages). The use of multiple fake agencies helped to obscure what Zirconium was doing. Each agency bought small amounts of traffic on a regular basis. The more agencies were involved the greater the returns for Zirconium and the more accepted the group became.
Zirconium then created relationships with the owners of landing pages. The traffic they had purchased was resold to affiliate platforms. Some of these were legitimate agencies but some, such as Voluum and AdSupply have a history of supporting malicious campaigns.
Interestingly, Zirconium also set out to run its own campaigns across its network. It even opened it up so that anyone could push ads through this network which it called MyAdsBro. Confiant says that: “Going as far as to build a black-hat affiliate network shows the level of sophistication that they reached in their operations.”
In the blog, Dangu suggests that Kovter, another major malvertising platform, was one of those buying traffic from Zirconium though affiliate platforms.
What was Zirconium advertising?
Confiant has identified a large amount of the content that Zirconium was distributing. It used ads that promoted fake Adobe Flash updates for both Windows and Mac. Mac owners are beginning to become more security conscious. As the success of the fake Adobe Flash campaign waned, Zirconium targeted Mac owners with fake antivirus campaigns.
The campaigns also featured a number of tech support scams around Microsoft desktop products. It also used scareware tactics pretending to come from Microsoft and warning of malware on the users machine.
Operating at an enterprise scale
Reading the blog it is clear that Zirconium was operating as effectively if not more effectively than many large corporates. According to Dangu: “Confiant identified the legal entity fronting the Zirconium activity as Cape Diamond LP, a shell company incorporated in Scotland with partners in the Seychelles — Damitra Group LTD and Lamen Business LTD.” In addition to Scotland and the Seychelles, there was also a mailing address which points to a business park in Kiev.
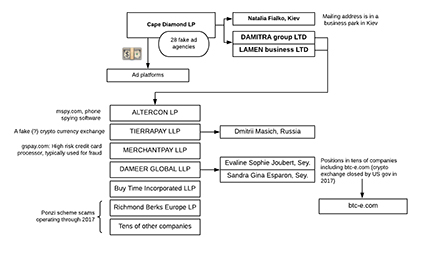
It built 28 fake ad agencies although Confiant only identified 20 as having been used. The companies identified as linked to Zirconium include phone spying software, a fake crypto currency exchange, a credit card processor and Ponzi scams. Many of these were disclosed by the company in its UK Corporate filings.
In addition to the company structure the scale of the social media empire is equally impressive. There are a number of Faceboo, Twitter and LinkedIn profiles. They were involved in coordinated campaigns designed to increase the reputation of various companies in the group. Interestingly, there is no evidence that they bought Twitter or other social media followers. This meant that in order to increase the reputation of the accounts, they had to employ a number of people to keep creating more and more content.
What does this mean?
Online advertising has been eating into the print and TV advertising market for some time. It hasn’t, however, managed to build the best of reputations. It is simple to commit click fraud and companies are still struggling to understand how effective online advertising through third parties can be.
However, there are vast numbers of small websites that depend on advertising from the ad networks. For many of these sites there is no alternative as they struggle to monetise themselves. Some have turned to crypto mining, often without telling their users that they are installing software on their devices.
Taking one billion ads out of the global network will cause a significant hiccup in how online advertising is seen. For smaller sites that were paid per click for ads on their sites, some will never see that money now that Zirconium and its agencies have disappeared. Others will find themselves scrambling to find replace sources of income.
Despite the scale of the Zirconium malvertising campaign there is a silver lining. Companies that worry about using online ad agencies and aggregators will see that the mechanism does work. The challenge for them is finding a trustworthy partner and understanding how to make advertising pay.