Security vendor Fortinet has revealed details of the MacRansom, Ransomware as a Service (RaaS) malware. The blog, written by security researchers Rommel Joven and Wayne Chin Yick Low, should act as a warning to Mac users to secure their devices. The researchers believe that this is the first RaaS targeted at Mac OS. The attack has a better than average chance of catching out Mac owners. This is because many have no endpoint security software on their devices believing that the platform is inherently secure.
This is a mistake. As Fortinet points out, Mac OS makes up less the 6.5% of the computers out there. As such, it is a small population for hackers to target. However, it is also seen as a higher earning user base. Over the last five years there have been many stories where sites charged Mac owners more than Windows owners. Examples of this are CNET outing Orbitz in 2012 and IBTimes calling out Home Depot back in 2014.
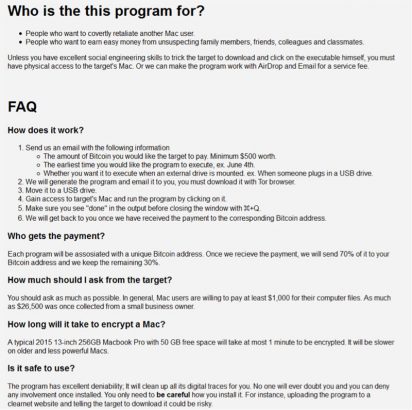
Now it seems hackers are going after Mac owners to see what they can get from them. In this case the authors of MacRansom say that: “In general, Mac users are willing to pay at least $1,000 for their computer files. As much as $26,500 was once collected from a small business owner.”
MacRansom available via a Dark Web portal
The security researchers found references to MacRansom on a Dark Web portal. They emailed the authors asking for more details. In their response the MacRansom authors claimed to be engineers at Yahoo and Facebook. This is an as yet unverified claim but certainly one that will raise eyebrows at both companies. Given its history of losing data this will be especially worrying for Yahoo. We sent an email to the Yahoo and Facebook press offices asking for their comment on this claim. So far there has been no response from either company.
The MacRansom authors say that they created the malware due to the lack of other attacks against the Mac platform. They also claim to have created their own Mac spyware that can be downloaded and used.
According to the blog the researchers proceeded to commission an attack. “We stated our requirements outlined by the author, such as the bitcoin amount for the target to pay, the date when to trigger the ransomware, and if it was to be executable when someone plugs a USB drive.” It took 10 hours for the attackers to respond and a couple of emails later the researchers were sent a sample of MacRansom.
Over several emails the researchers were also able to ascertain that the ransomware key was derived from the Mac serial number. They also discovered that the attacker is using a timezone on their messages that puts them in the Caribbean or parts of South America.
Is MacRansom as good as the authors claim?
The security researchers decided to test the efficacy of the malware. They took the claims made for it by its authors such as invisibility, deniability, speed and unbreakable encryption. They discovered a number of interesting and in some cases worrying things about the MacRansom. Two of the biggest concerns were around the way the files were encrypted and decrypted.
The researchers say: “A remarkable thing we observed when reverse-engineering the encryption/decryption algorithm is that the TargetFileKey is permuted with a random generated number. In other words, the encrypted files can no longer be decrypted once the malware has terminated – the TargetFileKey will be freed from program’s memory and hence it becomes more challenging to create a decryptor or recovery tool to restore the encrypted files. Moreover, it doesn’t have any function to communicate with any C&C server for the TargetFileKey meaning there is no readily available copy of the key to decrypt the files.”
They also question the ability of the malware author’s claim to be able to decrypt hijacked files.
It’s not all bad news
Any time there is a question mark over the ability to decrypt files, victims should be wary of rushing to pay. In this instance, however, Fortinet’s security researchers offer some hope. “It should not take very long for a modern CPU to brute-force an 8-byte long key when the same key is used to encrypt known files with predictable file’s contents.”
They also say that the ransomware is: “..far inferior from most current ransomware targeting Windows, it doesn’t fail to encrypt victim’s files or prevent access to important files, thereby causing real damage.”
There is more damning comments from the researchers. They say that this ransomware uses similar code and ideas from other OSX ransomware. This, they say, means MacRansom is just a copycat solution.
What does this mean?
For Mac users this means that if you were not taking the threat of ransomware seriously before, you should now. You should make sure that you backup your machine regularly to minimise the impact of an attack. As the attack can be set for a predetermined date, it is also important to have multiple copies of backups to be able to roll back before the malware was installed.
Corporate IT departments that do not have Mac’s covered by their endpoint software now need to do so. There has been an increase in the number of attacks on the platform and it cannot be left outside of IT security controls. The majority of Mac’s inside an organisation will be BYOD so it should be possible to enforce the same process on them as on Windows machines. After all, there is now a choice of several endpoint security solutions for the platform.
Interestingly the researchers do not take a stand on pay or don’t pay. However, they question the ability of the MacRansom authors to decrypt infected machines. That means that paying is unlikely to get files back. In this case it won’t take many fails before the authors are unable to get anyone to take on their software.
Despite all of the criticism we’ve seen poorly written ransomware in the past evolve to be effective. In this case they will need to do several things. They need better encryption, a command & control mechanism and prove they can decrypt files. None of this is insurmountable and with relatively little effort compared to the potential rewards. MacRansom might not be a real threat today but it will be important to monitor how it evolves.