This was not the typical ‘find the breach and identify what the attackers were after’ scenario.
Cyber security teams dealing with a cyber-attack are focused on getting a business back up and running. Storing evidence to a forensically acceptable standard is not high on their agenda. This means that law enforcement often find it hard to prosecute criminals at a later date. It is part of the reason that prosecutions for hacking have fallen for the last two years in the UK. That fall comes despite a rise in cybercrime.
There were initially 232 points on offer. However, an NCA spokesperson said “We removed an element so it ended up out of 200, the winning team got 187 which is really good. It was a close win as the runners up were only a couple of points behind.”
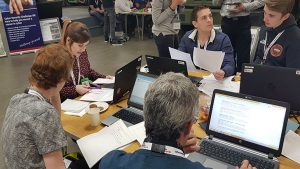
The competition was won by Team Warrior (photo above).
What was the NCA scenario?
UDP tanks is an MOD contractor. It has designed parts for the Challenger 2 tank. Its latest design uses a modular approach that speeds up repairs to a damaged tank.
The CEO received a blackmail letter telling him that the company data and IP has been stolen. He calls in the security team to track down the breach and discover who did it and how.
To win the challenge the teams had to investigate everything around the breach. This meant:
- Examine the IT logs to identify who downloaded the data
- Search the office to find the device that data was downloaded onto
- Examine USB devices and a laptop for evidence without destroying or changing it
- Identify the person who stole the data
Not as simple as it sounds
It sounds simple but it is far from that. It required the competitors to understand how to collect and preserve evidence. This included how to make identical copies of hardware such as hard disks and USB devices without risking contamination of the evidence. They then had to work on those copies when looking for information about the hacker.
The tests also required gathering data from outside of the IT departments domain. This included getting access to door logs and video from security devices. Examination of these would point to the key suspect and eliminate other people who they had tried to frame.
The NCA said: “Each of the areas we wanted them to explore had descriptors and within each had a scoring element attributed to this. Teams were then allocated marks based on the action they took.” An example of this is given below where the maximum score is 6 points.
| Examination of USB 2 | 0 | No USB identified or No examination conducted. |
| 1 | Examination conducted without imaging the device first. | |
| 2 | As above but imaged. | |
| + 1 | Notes taken during examination | |
| + 1 | Device opened using the Password from the Post it note. (If the Post it is not used and password is supplied they cannot get a point) | |
| + 1 | Identified documents taken from the victims computer. | |
| + 1 | Identified that this was the device used in the attack. |
The winners and a place in the Masterclass finale
The winning team were Team Warrior. Four of the five members of the team are students. The other member of the team is retraining for a career in cyber security.
Team Warrior was:
- Rhiannon Eason
- Stephane Ciolino
- Simon Gurney
- Sam Wedgwood
- Aiden Devrell
10 people were selected for a place at the Masterclass finale in November. They were picked for their combination of technical skills and soft skills, using the NIST framework for guidance. They are:
| Team | Name |
| Foxhound | Giles Pearson |
| Warrior | Simon Gurney |
| Scout | Sam Leonard |
| Scout | Bekalu Terefe Zenebe |
| Scorpion | Kinga Kieczkowska |
| Challenger | Logan King |
| Warrior | Sam Wedgwood |
| Foxhound | Christopher Williams |
| Challenger | Tom Brook |
| Scimitar | Edward Trist |
What does this mean
In the middle of a cyber-attack it is not easy to be forensically aware. Evidence has to be preserved to the standards acceptable by a court. If not, it is hard to prosecute a hacker. Cyber security teams already gather the information required by the main board about any attack. They now need to take the next step and be able to present the evidence to the police and prosecutors.
Part of this means that corporate legal teams need to get more deeply involved with cyber security. They have to teach them what is required and how it has to be done. It also needs new processes inside organisations that are focused on preserving evidence.
Cyber security teams will also need access to systems outside of their control such as door logs and security video. In this competition, both were an important part of the investigation. They will also need the right tools to capture and preserve evidence such a no write duplicators for storage devices.
For many organisations this means more investment into their cyber security teams. While some will baulk at the idea, without it, there will be little chance of prosecuting hackers.

























