The latest IBM X-Force Threat Intelligence Index is a mix of the bad, the ugly and maybe just a glimmer of the good. It is often too easy to focus on the bad and the ugly and not the good. The report shows that new records were set by several types of attacks. However, IBM customers monitored by X-Force actually saw a drop in the number of attacks compared to 2015.
A glimmer of light in the dark? Perhaps. IBM believes that: “The reduction in attacks could mean attackers are relying more and more on proven attacks, thus requiring fewer attempts.” There are several other views. Attackers are changing their attack vectors. They are now investing more time in attacking the personal technology of employees. As Bring Your Own Device (BYOD) grows, successful attacks lead to more chance of compromising the business.
Another view is that the attacks have moved downstream and out of the sight of IBM X-Force. Why waste effort attacking a large organisation head on. It is often far easier to compromise small suppliers and business partners. With digital transformation leading to greater automation and integration of the supply chain, those smaller players become gatekeepers to corporate systems. Company are not investing enough in supporting the supply chain when it comes to cybersecurity.
The full report can be downloaded from here (registration required)
A year of new records
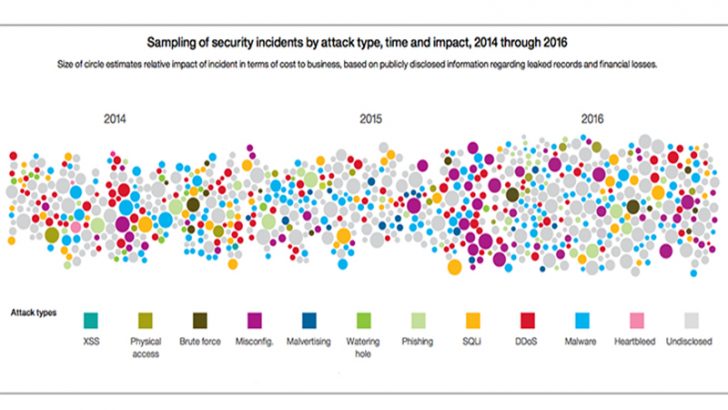
2016 was a year of records. Data breaches saw a new record of leaked records. Over 4 billion records were leaked in 2016 which is more than 2014 and 2015 combined.
Another record setter is Distributed Denial of Service (DDoS) attacks. This was driven by Internet of Things (IoT) attacks. Many IoT devices have little to no effective security and are outside of the control of IT security teams. This makes them easy targets for hackers who then enrol them into botnets. The size of the attacks has rocketed in the last few years. 2016 saw the first DDoS attack of 1Tbps. It is likely that 2017 will see the first multi Tbps attack as these attacks continue to grow.
Spam continues to be a serious problem. In 2016 and earlier this year coordinated actions by law enforcement around the globe saw several networks taken down. Despite this, spam has continued to grow. In 2016 it was up more than four times the previous year. More than 44% of those emails containing malicious attachments. 85% of those attachments were ransomware which has earned criminals significant sums of money.
Spear phishing has also been on the rise and has given way to new attacks. The most high profile of these is Business Email Compromise or CEO Fraud. This attack persuades companies to send money to accounts controlled by hackers when they think they are paying legitimate suppliers.
Security researchers uncovered a record number of vulnerabilities that were reported to vendors. The vast majority were patched within a reasonable timespan. However, it also became apparent that governments were sitting on a lot of undisclosed vulnerabilities. A number of these were stolen by hackers from the NSA and then made public.
Who was breached the most?
IBM is only able to give numbers around publicly disclosed security events. As such the data may not be wholly accurate. As we approach GDPR in 2018 we will see more disclosures and that will drive some of these numbers much higher. This is good news as it will provide a more accurate view of what is really happening across different industry sectors.
IBM says that more than 3.3 billion records were breached in attacks against companies in the Information and Communications space. This was over 8 times more than the number two sector which is government. This number has to be looked at with some care as historical disclosures will have inflated those numbers.
What are the top five targeted sectors?
When it comes to attacks the top five sectors were:
Financial Services: Attackers are after the large volume of Personally Identifiable Information (PII) held in Financial Services databases. The data can be traded and also locked up with ransomware providing the attackers with two lucrative attacks in one.
Information and Communications: These company hold large databases on their customers which includes payment data and PII. Governments are pressuring these companies to capture and store increasing amounts of data to help fight crime and terrorism. This data provides attackers with a treasure trove of personal data that people will pay not to have exposed.
Manufacturing: Some of the attacks are about disruption while others are after intellectual property. The risk of attack is one of the reasons why this sector is seen as being among the slowest to move to cloud computing.
Retail: PII and card data is held by retailers along with purchase histories. This allows attackers to craft targeted attacks using purchase histories. Victims often believe that these are real offers from retailers they have used in the past. Instead they are malvertising that sends the victim to other sites where malware such as banking trojans and ransomware are downloaded onto their computers.
Healthcare: Poor IT security in the healthcare sector has made it a magnet for attackers. Many of those attacks use ransomware to extort money from a sector that cannot afford to lose patient data. The data itself has a significant value as in many countries it is tied to healthcare insurance. This is resulting in an increase in fraudulent claims that will continue to increase.
Inside or outside: Where are the attacks coming from?
The insider threat has always been greater than the external attacker. Many companies, however, choose to play down the threat from their own staff. IBM says that there is a third actor when it comes to attacks, the inadvertent actor. IBM defines the latter as: “insiders who do not mean harm but fall prey to social engineering schemes that grant access to outside attackers.” This is often the result of spear phishing attacks that look to exploit the individual.
In both financial services and healthcare the insider threat is greater than the external threat. Interestingly in both cases the inadvertent actor is the biggest risk. In financial services over 50% of attacks are down to the inadvertent actor. In healthcare it is around 46%.
For the other three most attacked industry sectors the external threat represents over 90% of the attacks that they face. Is this because employees are better educated or more cybersecurity aware? It is unlikely. The more obvious explanation is that those industries where insider attacks are prevalent are more susceptible to phishing and other similar attacks on staff.
What does this mean?
For once that is not as easy a question to answer as it might seem. The average number of security incidents is down 48% from 2015. This comes despite a slight increase in the number of events recorded by companies. It shows that cybersecurity is getting better and companies are putting in place better training and mitigation systems.
However, given the number of records set by types of attacks it means that the attacks have shifted somewhere else. That is the supply chain and individuals. Security teams need to do more to help staff especially those who could be the inadvertent insider. Better tools and training for individuals is one option.
It is also important that IT security teams are made available to help smaller partners in the supply chain. This will help mitigate attacks from that source as digital transformation plans increase system integration and automation.