
Researcher Bjὃrn Ruytenberg, from the Eindhoven University of Technology, discovered Thundersky. Ruytenberg has published a paper detailing Thunderspy which includes the vulnerabilities, affected machines, partial mitigations and exemplary exploits. It makes for interesting reading and shows how dangerous and effective Thunderspy is.

According to Ruytenberg: “Thunderspy is stealth, meaning that you cannot find any traces of the attack. It does not require your involvement, i.e., there is no phishing link or malicious piece of hardware that the attacker tricks you into using. Thunderspy works even if you follow best security practices by locking or suspending your computer when leaving briefly, and if your system administrator has set up the device with Secure Boot, strong BIOS and operating system account passwords, and enabled full disk encryption. All the attacker needs is 5 minutes alone with the computer, a screwdriver, and some easily portable hardware.”
What do we know about Thunderspy
Thunderspy is an evil maid attack. Leaving a device with a Thunderbolt port unattended and allowing an attacker to gain physical access to it, means they can access the data. It doesn’t matter if the device is locked or in sleep mode or if the data is encrypted. All the attacker needs is access to the computer.
Evil maid attacks are where people leave their computer on a desk in hotel rooms. They close or lock the screen and go for breakfast, dinner or a drink. It allows the evil maid to access the room to launch the attack on the computer. It is an effective and straightforward attack.
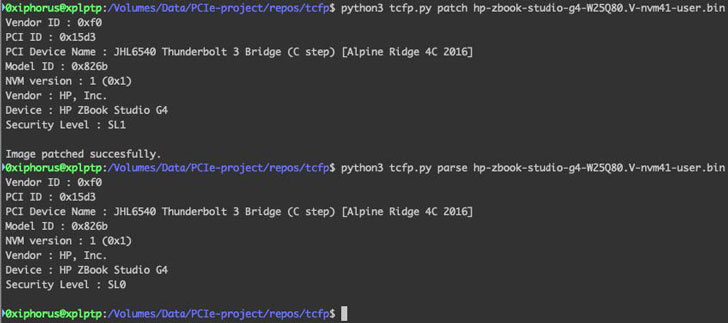
Ruytenberg has identified seven vulnerabilities:
- Inadequate firmware verification schemes.
- Weak device authentication scheme.
- Use of unauthenticated device metadata.
- Downgrade attack using backwards compatibility.
- Use of unauthenticated controller configurations.
- SPI flash interface deficiencies.
- No Thunderbolt security on Boot Camp.
For each vulnerability, there are multiple exploits and in the paper detailing Thunderspy Ruytenberg also provides some exploitation scenarios.
Intel dragged its feet and didn’t do full disclosure
One of the worrying things here is Intel’s response. Ruytenberg has published the disclosure timeline to Intel about the different vulnerabilities as they were found. He states: “We disclosed vulnerabilities 1-5 to Intel on February 10. They wrote on March 10 that their engineering team confirmed the vulnerabilities, and that vulnerabilities 3-5 were new to them. After further research, we disclosed vulnerability 6, which Intel confirmed on March 17.”
Hardware vendors generally alert all their OEM/ODM partners once vulnerabilities are confirmed. This allows them to develop patches and ship them in a coordinated process. Unfortunately, it seems that Intel decided not to do that. It took several emails before Intel started to pass the information along. Even then, Ruytenberg identified affected parties that Intel did not alert to Thunderspy.
He says: “In our first email we asked Intel to promptly notify affected parties, in coordination with us. However, Intel did not take any action and finally, after several email exchanges, listed only 5 parties whom they would inform. We then sent them a list of other parties we had identified as affected, including 11 OEMs/ODMs and the Linux kernel security team. Eventually, they notified us that they informed some parties on March 25 about the vulnerabilities and upcoming disclosure, without giving us details of what this information consisted of and whom exactly they contacted. We reached out to several more parties after realizing that they had been skipped by Intel.”
Enterprise Times has asked Intel for more information. So far, beyond saying there is a document addressing this, Intel has failed to provide a copy.
What about Apple?
Ruytenberg says that all Apple Macs released from 2011 onward, except for Retina MacBooks, are vulnerable to Thunderspy. Ruytenberg says that his team provided Apple with the details of vulnerability seven on April 17. It is the only vulnerability that applies to Apple devices.
Importantly, it only affects Apples when users are running Boot Camp to run Windows or Linux. This is because doing so disables the Thunderbolt security. A lot of security researchers and developers use Boot Camp so that they can develop and test multiple operating systems on a single device. Thunderspy may cause them to rethink this approach.
Apple gave the following response over the disclosure. “Some of the hardware security features you outlined are only available when users run macOS. If users are concerned about any of the issues in your paper, we recommend that they use macOS.”
Protecting against Thunderspy
According to Joseph Carson, chief security scientist at cybersecurity firm Thycotic, there are things users can do to protect themselves.
“The Thunderbolt flaw exposed on millions of computers is a serious issue as it allows an attacker only a matter of minutes to bypass the device security that keeps unauthorized users out. Though luckily for this attack, it does require physical access and requires visible tampering so it can only happen when an attacker is alone for several minutes with your computer.
“This means leaving your computer for only a few minutes gives an attacker the ability to gain access to your data, activity and accounts. It might be worth making it a little bit more difficult and placing tamper-resistant stickers over your device screws to at least make any tamper more visible, though this by itself is not full proof. Making sure to log off when you leave your device unattended makes it more difficult, though again, not impossible for the attacker to gain access. Anything you can do to force the attacker to take more time being successful for such attacks increases the risks of them getting exposed. At this time, I have not seen any evidence of this attack being used though it does raise questions to how long attackers may have known about this.
“Unfortunately for this attack, there is no easy fix and any vendor’s hardware exposed by this attack will need to come up with creative ideas to make it more difficult and fully resolve the vulnerability.”
Enterprise Times: What does this mean
Many users see vulnerabilities as a software issue, and by that, they mean the operating system or application. What has become evident over the last five years is that the firmware inside computers is just as open to attack as software on the device.
The Meltdown and Spectre attacks against computer processors from several vendors caused chip vendors to rethink their design processes. Thunderspy is likely to have the same effect. The introduction of Kernel DMA Protection in 2019 mitigates some of the impacts of Thunderspy. However, it does not remove it entirely.
Thunderspy is also likely to impact future technology standards such as USB 4 and Thunderbolt 4. Ruytenberg says that both of these standards will require a silicon redesign. With both expected to ship in computers this year, it means that OEMs/ODMs will have to make some hard choices. Do they delay the release of new hardware or ship with a known vulnerability?
Even if Thunderspy is fixed in silicon, the problem will be the millions of devices that are currently in use. This is not an attack that will go away soon.


























