
Security vendor Zscaler has reported a spear phishing campaign where MS Office documents contain macros that install malware on user machines. The two pieces of malware identified by Zscaler are Kasidet and Dridex and early indications are that one of the IP addresses being used to distribute the malware is located in Russia (158.225.6.128).
MS Office macros a long standing security problem
The use of macro code to spread malware is nothing new and goes back over 20 years. What is making this current campaign of using spear phishing effective is that users seem willing to keep clicking on warnings over macros. The bulk of the current campaign seem to target people who may have control over handling invoices, refunds, orders or returns. The user opens the document in the email and if their Office is in default mode they are asked to allow the macro to run. With a single unguarded click the macro is enabled and the machine infected.
What is interesting is that Zscaler reports that the macro has been obfuscated to make it hard to spot. In their press release Zscaler publishes the macro code and shows that it contains one of three different hardcoded URLs. As these get published and blocked it is likely that the malware writers will add new URLs. The three that have currently been identified so far are:
- armandosofsalem[.]com/l9k7hg4/b4387kfd[.]exe
- trinity.ad-ventures[.]es/l9k7hg4/b4387kfd[.]exe
- 188.226.152[.]172/l9k7hg4/b4387kfd[.]exe
The banking malware Dridex has been successful over the last year in using this approach to infect a lot of machines. According to Zscaler the success of this route has now seen Kasidet added to the malware that is being distributed and it may not be the only addition. There are already reports coming out of other security vendors that macros are being used to distribute different strains of Cryptolocker malware.
Zscaler analysis of Kasidet
Kasidet is likely to be a fairly new malware for many security teams. It was detected by Symantec back in 2014 and by September 2015 Trend Micro was reporting it as a major problem. Originally designed as a Distributed Denial of Service (DDoS) bot, Trend Micro identified new features including the ability to scrape credit card data had been added to the software. That report focused on Point of Sale (PoS) systems but with the development of a commercial builder for Kasimet the malware is now moving into the wider market.
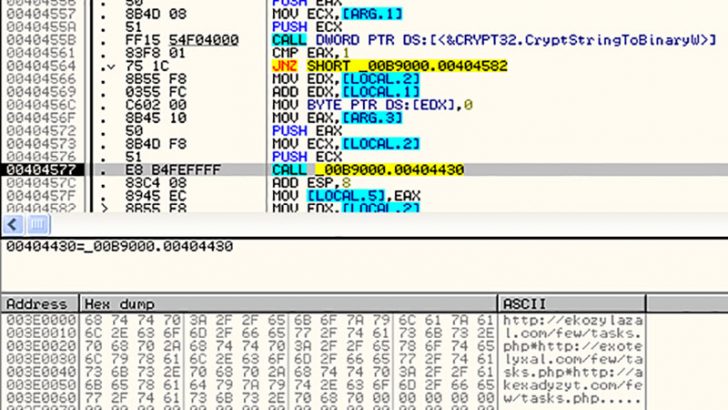
One of the interesting pieces of information from the Zscaler research is that the Kasimet variant being used in this campaign should be possible to spot or at least detect quickly. Perhaps the most obvious thing to look out for is that Kasimet has the string “Y1FeZFVYXllb” hardcoded into it and also uses that string to create an entry in the Windows registry. An automated search of the registry will help security teams detect the infection and is something that could be done on a nightly basis for any machine taking credit card data.
The writers of Kasimet have enabled a number of antiVM (Virtual Machine) techniques to see if it is being installed natively on the hardware or inside a VM. IT does this by scanning for various Windows APIs and through the Windows Registry.
There are two techniques used by the malware to steal data. The first is to use memory scraping to take data from PoS systems. This is done by checking any memory space used by a number of system functions. The second approach is to hook to the browser and this is where Kasidet is having good success on users machines. Internet Explorer (all versions), FireFox and Chrome are all susceptible but Zscaler has not said if Microsoft Edge, its latest browser is also affected.
In an interesting twist, should the malware detect that the user is located in Russia then it deactivates the information stealing routines. This further strengthens the view that this is Russian malware that is being distributed with great success, according to Trend Micro, in countries such as Japan, UK, Taiwan, France and the US. There is also a hard coded set of command and control (C&C) servers which can be blocked by administrators. At present these are:
Conclusion
The success of macros as a way of spreading malware more than 20 years after we first saw this method continues to surprise security teams. Part of the reason for the success is the use of macros inside organisations to automate repetitive tasks which means users do not see them as a problem. The failure of user security awareness programmes to help them realise the risk is helping this attack vector to flourish.
Anytime an attack vector is successful cybercriminals will continue to exploit it and that is what we are seeing here. The evolution of the attacks from Dridex to target banking data to Kasidet to steal credit card data is a natural one. It won’t be long, however, before we see warnings about the same approach being successful with the spread of Cryptolocker variants.
One of the surprises is that the writers of this particular strain of malware are using a small number of hard coded C&C servers, URLs and identifying strings. These make it easy for the security industry to build detection agents and to limit the spread of the malware. The other surprise is that they have excluded data gathering from anyone inside Russia.


























